What can you learn from the hacking of the Office of Personnel Management?
On June 5th a US agency you had probably never heard of (I hadn’t) called the Office of Personnel Management (OPM hereafter) confessed to an enormous breach, which had compromised the records of millions of federal employees. The OPM acts as a kind of centralised human resources for US government departments, and hence collected lots of data on all those employees. Even worse, it held data on people who had applied for government clearances. In the US, as in the UK, you are forced to disclose a lot of personal information when applying for clearances (and I mean a lot – basically everything about yourself, including those things you’d rather forget) as the aim is for the government to be sure it can trust you and you aren’t likely to be easy to blackmail. Although there has been no official announcement, lots of unnamed sources are pointing the finger at Chinese state backed (or state employed) hackers.
What’s the impact?
Hard to say. As I commented in that VoA article linked above, we typically have associated state sponsored hacking with either the theft of intellectual property or targeting of more traditional government and military information. However details on state employees are incredibly attractive to a spy organisation. Imagine if SIS (the UK spy agency) were presented with a list of everyone who worked in Russian government departments, as well as those who had applied for clearances. Pretty handy. Want to recruit someone in the Russian Ministry of Defence? To the database! Not only do you have names, addresses, contact information but also details of financial records and much much more personal information in the case of clearance applications.
All this data is gravy to spooks. It can help them craft extremely good phishing (i.e. fake) emails in an attempt to compromise an organisation through hacking, but equally is fantastically useful for old fashioned physical spying, whereby you approach someone, build a rapport with them and over time move them to spying for you. Knowing a lot about them, notably things like expensive hobbies, sexual preferences etc can aid this process, or you can move quickly to simple blackmail. US government employees are going to have to be extra suspicious for many years to come about that nice Chinese couple they met on holiday in Mexico, and who sat at the table next to them for dinner two nights in a row, and oh didn’t they have the funniest story about …
Anyway, I digress. It’s pretty disastrous, presuming it was Chinese spooks. If it were just Chinese criminals, then it is still pretty disastrous because a) the Chinese spooks can just buy the information from the Chinese criminals (or probably just get it without paying), and b) all those US government employees are likely be victims of identify theft, fraud, phishing and whole variety more of fun criminal activities.
Response wise, it’s tough. Whilst the US has shouted loudly about Chinese state backed economic espionage, this falls more squarely into the category of legitimate spying (from a Western perspective at least). Obama can’t complain too loudly, as undoubtedly the NSA and CIA would love to have (and indeed may have) the same sort of information on Chinese government organisations.
But what can I learn from this?
Quite a bit. The root cause of security failures at the OPM is ultimately underspending on IT infrastructure, as well as specifically failing to invest in security measures. As the head of the agency said testifying to Congress, the hack had been decades in the making. A quote from a Inspector Generals review of the OPM IT systems is revealing:
“OPM does not maintain a comprehensive inventory of servers, databases, and network devices. In addition, we are unable to independently attest that OPM has a mature vulnerability scanning program.”
Poor asset management is a gift for hackers. You will be familiar with the mantra of patch, patch, patch. If you don’t know what you have out on your estate how can you patch it? Effective asset management underpins good cyber security. Also it appears OPM have very out of date systems. This is a common problem, especially at large organisation. The UK government paid Microsoft for a year of extended support for Windows XP, when support officially ended in 2014. That support has not been renewed this year, despite the admission of the fact that there are many UK government organisations still running XP desktops, with the total XP install base still numbering in the many thousands. Support for Windows Server 2003 ends imminently, and yet there are many, many organisations who will not be ready to migrate away from the now obsolete platform. Once an operating system is no longer supported, there will be no security fixes for any newly discovered vulnerabilities.
So from the OPM hack you should take away this fact; Invest in your IT infrastructure. Do not get stuck on outdated software.
At The Cyber Security Expert we like to keep things simple. Our mantra for building a solid foundation of security is:
- Know your network
- Know your assets
- Train your people
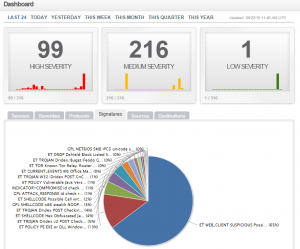
Another lesson; OPM detected the attack when they began doing network security monitoring. Security monitoring, or intrusion detection as it is also known, is a powerful tool. If you ‘know your network’ you can make sensible decisions about what network traffic you allow in and out to the internet, where you might put additional security measures in place (such as web proxies) and you can do effective network security monitoring.
I am often asked by clients ‘how would I know if I were hacked?’. Without security monitoring, you won’t.
So, make life for the attackers as hard as possible. Do IT management well. Invest in the new technologies, and plan migrations away from operating systems before they become unsupported. When you’re ready to invest in specific security, decide what would help you the most; where are your vulnerabilities, do you have good visibility of your network?
Thanks for reading. Any questions, twitter, or use the contact form. Also if you liked this post why not share it on Twitter or LinkedIn using the link at the top?
Rob