Ask The Cyber Security Expert: Dealing with suspicious files and links
A few weeks ago The Cyber Security Expert explained how you can spot suspicious email. Dealing with suspicious emails, which may have attachments or embedded links is something anyone working in security does everyday. We dragged The Cyber Security Expert from his Buffy Fan Fiction writing group, and got him to answer some questions about what you can do when dealing with suspicious files and links.
Suspicious Email
Just to recap, for those at the back.. Never ever click on links, or open attachments, in emails that exhort you to do just that. Seriously, never. Go read our post on suspicious email again if you’re not sure why. But anything to do with finance, online accounts, suspended access, parcel deliveries and so and as forth, which want you to open an attachment or click on links, are bad. If you are worried about a bank account, or PayPal, or any other online service, visit the site directly by typing the web address (e.g. www.mybank.com) into your web browser of choice, and login.
It is trivially easy to spoof the source of email, and to dress them up to look legitimate, and to lead you to a fake login page and snaffle your username and password.
Ok, that’s done. Lets move on.
Checking suspicious files
You have a suspicious file. Maybe it came by email, turned up a USB drive or was downloaded. The first thing to do is check it with your local antivirus. If it flags it as bad, delete and move on.
However, you might still not be sure. Handily for security analysts everywhere there are some really good online tools you can use. The first, and the one that will become close to your heart is Virustotal.
Virustotal rocks. It is a Google company, though that is not immediately obvious from the branding. Virustotal lets you upload files, and then it then scans that file with a range of antivirus products (currently 54).
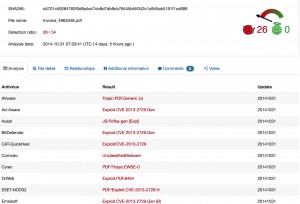
A screen shot from Virustotal (click to enlarge). This is a sample pdf that is clearly bad.
If you get green across the board with Virustotal you have confidence that the file is probably not malicious (it’s not a certainty, but its a very good place to start). If you get hit with one or more of the AV products, then you have a level of assurance that your suspicions were justified.
There is more to VT than just that – you can search it, and if you pay them some money do a whole range of useful things. But if you just want to see if a file is bad or not, it’s an extremely useful tool. Free, and no need to sign in.
If you want to do something more sophisticated, and see what actually happens when you open a suspect file, a good next port of call is Malwr. Malwr takes your uploaded file, and opens it in a controlled Windows environment (called a sandbox). You then get a report detailing what happened, including what other files, if any, were created, and any network connections made. You also get a screenshot. Depending on your level of knowledge this info can let you make a reasoned decision about the legitimacy, or otherwise, of the file.
What about links?
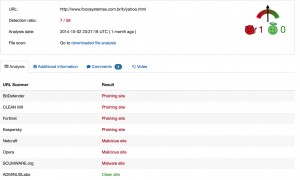
Well, there is always Virustotal! Yes, Virustotal does links too. Simply select URL rather than file (above the search box), paste in your link and away you go. As with files, it will give you an output from a large range of antivirus products
The screenshot above is an example output from a site that was being used for phishing.
If you want to do something a bit more sophisticated, try URLQuery. In a similar manner to how Malwr works with files, URLQuery visits a website for you, records and report on what happens and gives screenshots (useful as you can see for yourself what the content of a website is, without having to visit it from your computer). URLQuery reports contain a lot of useful information, including showing if the site is on any blacklists (for instance as a known bad site), and also if any malicious content is delivered.
Finally, for a broad brush view of whether or not a site is malicious, there is Google Safebrowsing. This functionality is built into Google Chrome, but anyone can access it. You need to enter the site you want to visit into the link itself. For instance this is how you would check this website:
http://www.google.com/safebrowsing/diagnostic?site=www.thecybersecurityexpert.com
Add the site you want to review after ‘site=’.
Google Safebrowsing will report if the website in question has been known to host malicious software, and is another useful indicator of the trustworthiness, or otherwise, of a website.
Any more?
There are lots of other tools you can use when investigating cyber security incidents, and we will continue with blogs on this theme with more guidance. The tools above will enable you to verify links, and attachments with confidence and help out co-workers and family members with the same. If nothing else remember the mantra ‘Virustotal is my friend’.
As always, if you have questions please get in touch! Find us on twitter, or use the contact form.
The Cyber Security Expert